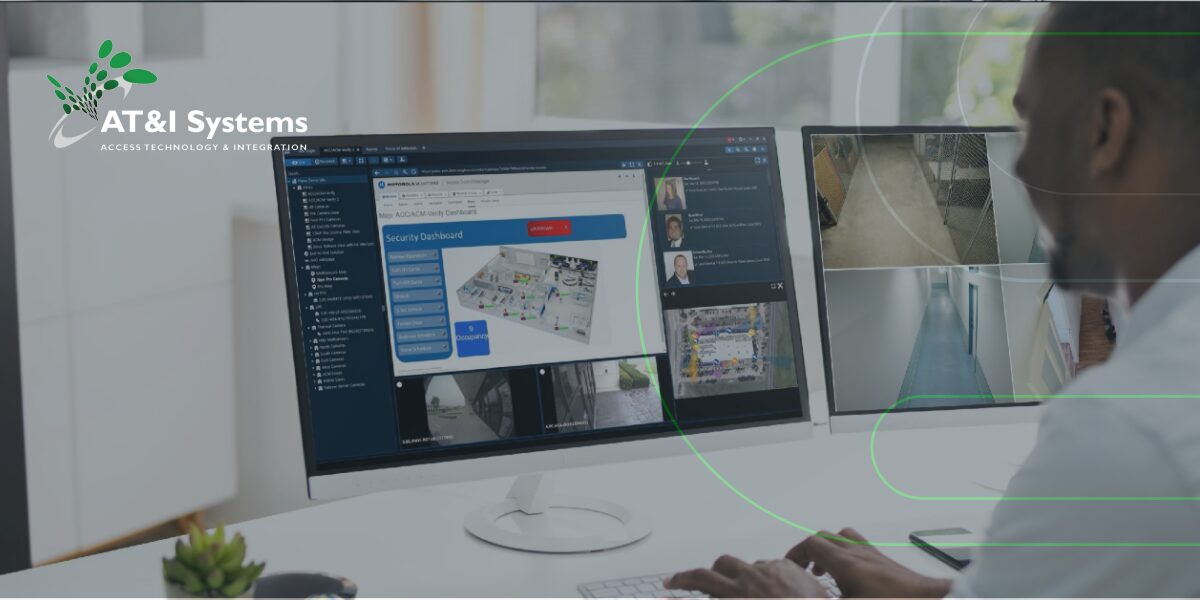
AT&I SYSTEMS IS FOUNDED ON A CORE SET OF VALUES THAT POSSITIVELY IMPACT OUR TEAM, OUR CLIENTS, OUR PARTNERS, AND OUR WORK.
Latest News
Press Releases

Amerant Bank Enhances Security with Omnilert AI Surveillance Technology

Amerant Bank Selects Omnilert AI Technology for Enhanced Video Surveillance Security
Discover Fresh Content Every Month
A Comprehensive Guide to Commercial Gate Systems for Property Managers
Understanding Gate Types, Security Features, and Selection Criteria to Protect Your Property and Streamline Operations Commercial properties face a variety of security challenges that require more than basic perimeter control. Modern gate entry systems serve as both...
Why Should We Consider Upgrading Our Access Control System?
Exploring Access as an Amenity How often do you update your access control solutions? The right system can make all the difference for security and ease of access. Modern access control systems enhance security and the overall experience for residents and guests. They...
Visual Firearm Detection for Safer Schools & Workplaces
Explore This Proactive Approach to Protect Commercial Spaces Safety threats are evolving quickly, and commercial spaces from schools to businesses need smarter, faster, and more reliable tools to protect people and property. One of the most promising innovations today...
Common Security Mistakes Businesses Make & How to Fix Them
Why Risk Assessment in Security is Crucial Security threats can pose significant risks to small and medium-sized businesses, as well as commercial landlords. Many organizations fall into common security pitfalls that leave their assets, employees, and customers...
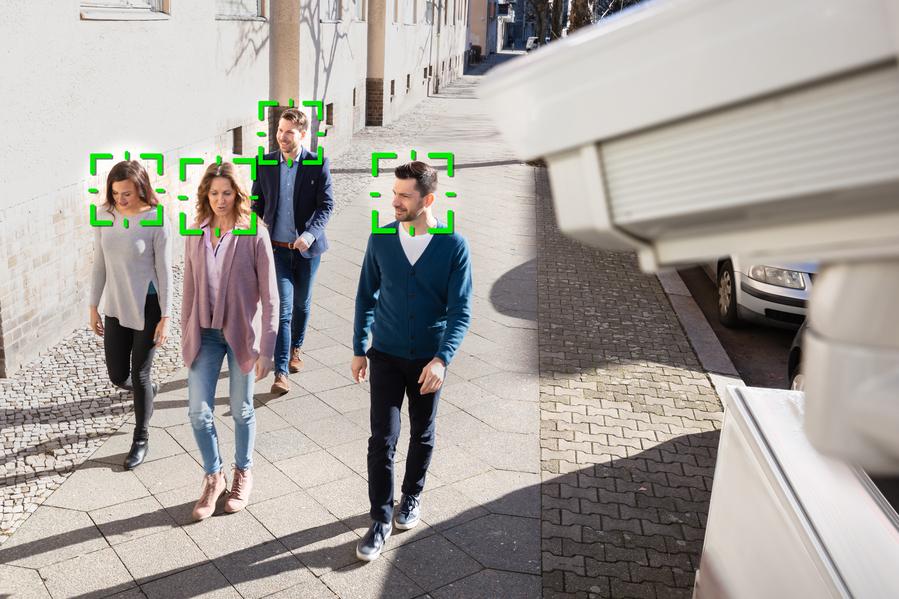
The Role of Video Surveillance in Preventing Theft & Vandalism
Why Video Surveillance for Businesses is Essential Protecting assets and ensuring safety has always been a top priority for business owners. Whether you manage a retail store, warehouse, or commercial property, theft and vandalism pose significant threats. Investing...
Why Every Business Needs Commercial Security Systems for Risk Mitigation
Protecting assets, employees, and customers is more critical than ever. Commercial security systems provide an essential layer of defense against theft, vandalism, and other security threats. Whether you manage a small retail store or a large corporate office,...
How Access Control Solutions Improve Workplace Security & Efficiency
Ensuring a secure and efficient workplace is essential now more than ever. Access control solutions provide businesses with the tools to regulate entry, track employee movement, and enhance overall security. By integrating modern gate entry security and biometric...
Modernizing Commercial Building Security with Keyless Access and Facial Recognition
Securing commercial buildings is more important than ever. As security threats evolve, so must the tools we use to protect people and property. The good news is that as threats become more sophisticated, so do the solutions. Modernizing your building’s security system...
The Importance of an Integrated Security System for Gated Communities
Gated communities are designed to provide residents with a sense of exclusivity, safety, and peace of mind. While the physical barriers of gates and fences serve as a first line of defense, modern security challenges demand more sophisticated solutions. This is where...